APK Tool A tool for reverse engineering 3rd party closed binary Android apps. It can decode resources to the nearly original form and rebuild them after making some modifications. It also makes working with an app easier because of the project like file structure and automation of some repetitive tasks like building apk, etc.
It is NOT intended for piracy and other non-legal uses. It could be used for localizing, adding some features or support for custom platforms, analyzing applications, and much more.
Features
- Disassembling resources to the nearly original form (including resources.arsc, classes.dex, 9.png. and XMLs)
- Rebuilding decoded resources back to binary APK/JAR
- Organizing and handling APKs that depend on framework resources
- Smali Debugging (Removed in 2.1.0 in favor of IdeaSmali)
- Helping with repetitive tasks
Requirements
- Java 8 (JRE 1.8)
- Basic knowledge of Android SDK, AAPT, and smali
So far we’ve been working with tools that are centered around Android developer and not reverse engineering. But now we’re going to download our first security tool. It’s a super popular tool and you can say that is part of the foundation of most Static Analysis Tools out there, this tool is called APKTool
Also Read : Install SDK Manager and Android Emulator On Android Studio
Install APKTool
Now the downside here is that you will be getting the last version available in this repository, not the actual last version. So now we have apktool installed on the system.
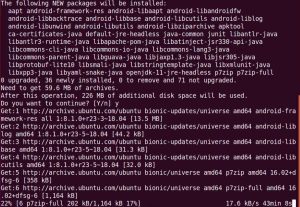
# sudo apt-get install apktool
Download Sample of APK from the popular APK website after apktool installation is finished
Once the download is complete, let’s go to the downloads folder and run apktool on the apk using the ‘D’ parameter so ‘D’ for decode the sample apk file. In my case, I have renamed the apk file a ” test “
# sudo apktool d test.apk

Also Read : ADB in Android Studio
Video Tutorial
That’s all, in this tutorial we have learned how to decompile APK files using apktool. We will have a look at this tool in more detail during the reverse engineering part of this Android series.


